A
AlixPartners
Cybersecurity is essential to hardware manufacturer operations. But in a globalized supply chain, a company’s security is only as strong as its weakest link (for instance, a single hacked vendor cost Applied Materials $250 million in 2023).
United Kingdom
Technology
To print this article, all you need is to be registered or login on Mondaq.com.
Cybersecurity is essential to hardware manufacturer operations.
But in a globalized supply chain, a company’s security is only
as strong as its weakest link (for instance, a single hacked vendor
cost Applied Materials
$250 million in 2023).
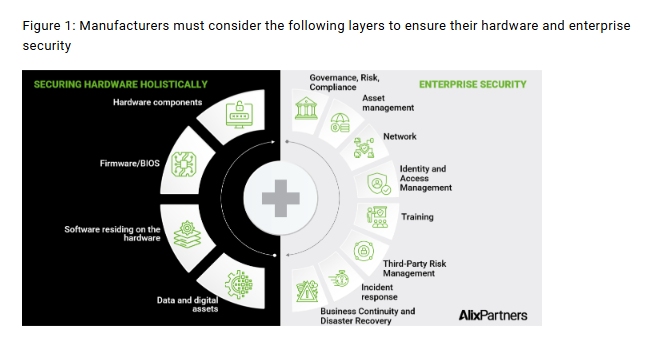
During such uncertain times, business leaders must stay vigilant
against evolving cybersecurity risks, though it’s difficult to
discern the best path to take. We have noticed that leading firms
are taking a holistic approach to address security across hardware,
software/firmware, data and digital assets, and even the AI-driven
solutions integrated into their products.
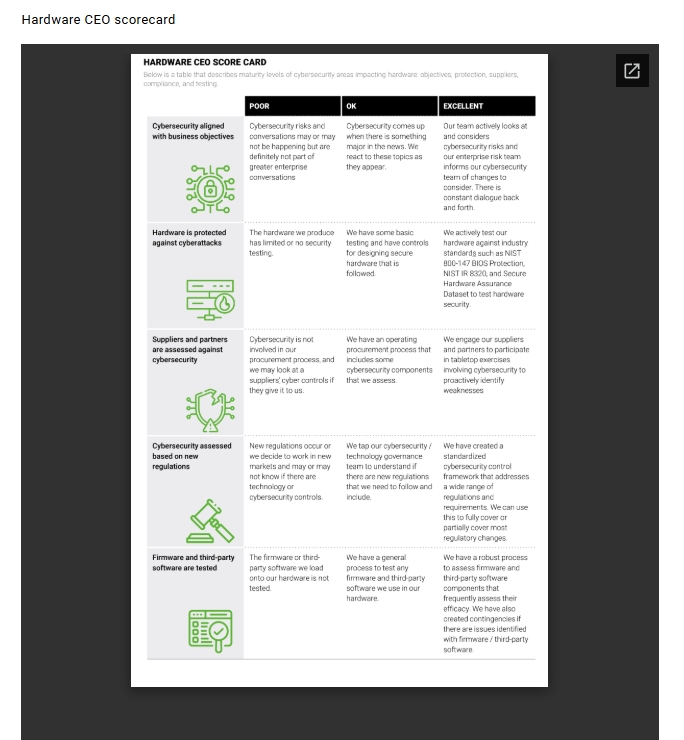
CEOs can ask themselves the following five questions to evaluate
their security programs and detect potential blind spots:
1. How do we align our cybersecurity risks to business
objectives?
While you cannot fully prevent cyber attacks, they do not need
to derail business objectives. Applying cybersecurity risk
management bidirectionally to enterprise risk management may help
organizations weather any storm by uncovering risks and preparing
solutions. This extension to existing processes ensures a more
efficient and proactive approach that can protect business growth
(and prevent devaluation).
Leaders should include cyber risks as part of greater enterprise
activities because of their impact on the company as a whole. Small
cyber events, such as the 2023 MSI cyber attack and the 2021 Acer
ransomware attack, resulted in stock price losses on breach
notification days. Cyber attacks have enterprise-wide consequences
and thus need enterprise-wide considerations through the risk
management process.
2. Are we adequately protecting our hardware against
cyber attacks?
Most organizations have basic controls to protect their
hardware, such as disabling USB access. However, hardware
manufacturers face additional regulatory requirements imposed on
third-party suppliers. Recently, the SEC increased requirements for
due diligence on suppliers, including cybersecurity controls.
Hardware customers are now asking their third parties for
corresponding cybersecurity assurances.
Such scrutiny is only increasing as emerging technologies, such
as AI, open new markets for hardware manufacturers. As demand for
these products grows, hardware buyers must evaluate the quality of
components, including those for security. Ensuring secure hardware
is a significant advantage for companies, as it minimizes faults in
delivered final products, making the business more reputable and
resilient. Businesses can leverage industry guidance such as NIST
800-147 BIOS Protection, NIST IR 8320 on hardware security, and
Secure Hardware Assurance Reference Dataset to boost their security
measures.
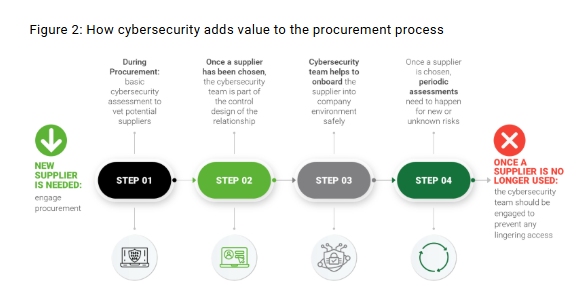
3. Are we looking at the cybersecurity maturity of our
suppliers and partners?
A single compromised supplier is capable of disrupting
operations on a global scale—the SolarWinds breach, for
instance, impacted Microsoft, Intel, and Cisco. As a result,
regulators are responding with new rules for overseeing third-party
cyber risks, such as Executive Order 14028 which mandates strict
security standards for government software suppliers. Ensuring the
cybersecurity of your vendors is no longer a priority, but a
business-critical necessity.
Recent instability in the market has caused many companies to
reevaluate their suppliers and supply chains. Hardware
manufacturers that prove their cybersecurity reliability will
maintain a competitive edge when companies look to make supplier
changes.
4. Are there additional considerations we need to make
for shifting regulations?
Regulations may shift in response to marketplace disruptions,
such as when an organization enters a new region or industry
sector. Companies should be wary of both the direct and indirect
impacts of regulatory changes. For example, as tariffs require
organizations to reassess their third-party suppliers, hardware
manufacturers must evaluate their third-party risk management
cybersecurity controls to prevent new weaknesses from entering
their environment.
When a company looks to make a change, whether it is through
acquisition, a new service line, or even a simple supplier switch,
there should be a cyber component present to cover the associated
risks to the business.
5. How do we ensure that the firmware and third-party
software we use are secure?
After securing their physical hardware, manufacturers should
scrutinize the firmware and third-party software of their products.
This includes interdependency reviews on third-party software. With
security controls for critical software components managed by other
teams on the vendor side, hardware companies should implement
strong Secure Software Development Lifecycle (SSDLC) processes to
review sources of risk.
Just as hardware manufacturers safeguard their businesses by
maintaining marketplace trust, they must also rigorously evaluate
the third-party vendors they depend on. As demonstrated by
incidents involving companies like Applied Materials, a compromised
vendor can disrupt operations or diminish your organization’s
intrinsic value if compromised firmware or software is integrated
into your products.
The content of this article is intended to provide a general
guide to the subject matter. Specialist advice should be sought
about your specific circumstances.
link
